容易设置分享华为防火墙路由模式部署
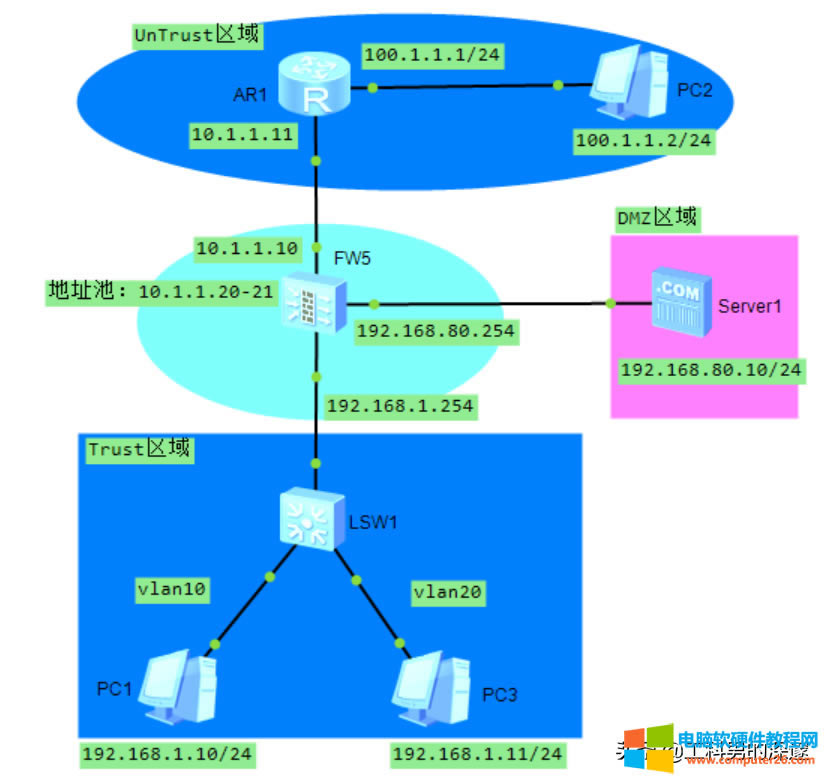
下面拓扑是防火墙的一种部署方式,按照网络规划,先配置好路由器、防火墙、核心交换机及各终端、服务器设备的IP地址。
1路由器R1的配置
[Huawei]sysname R1
[R1]interface GigabitEthernet 0/0/0
[R1-GigabitEthernet0/0/0]ip address 10.1.1.11 24
[R1]interface GigabitEthernet 0/0/1
[R1-GigabitEthernet0/0/0]ip address 100.1.1.1 24
[R1-GigabitEthernet0/0/0]q
ISP路由器上没有配回程路由,都是由防火墙上NAT进行转换的。
2配置防火墙的接口地址
[fw1]sysname FW1
[FW1]interface GigabitEthernet 0/0/1
[FW1-GigabitEthernet0/0/1]ip address 192.168.1.254 24
[FW1]interface GigabitEthernet 0/0/2
[FW1-GigabitEthernet0/0/2]ip address 192.168.80.254 24
[FW1]interface GigabitEthernet 0/0/3
[FW1-GigabitEthernet0/0/3]ip address 10.1.1.10 24
[FW1-GigabitEthernet0/0/3]q
验证配置结果
[FW1]display ip interface brief
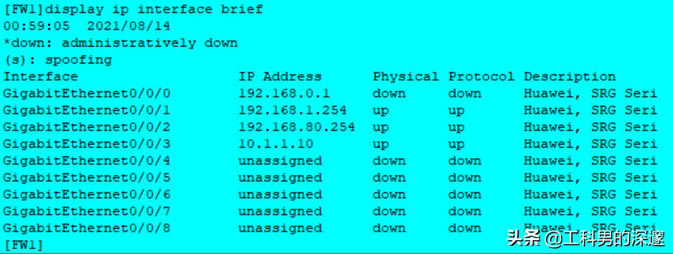
此时防火与各区域设备不能互通,接着下面的配置。
3把接口添加到防火墙安全域中
[FW1]firewall zone trust
[FW1-zone-trust]add interface GigabitEthernet 0/0/1
[FW1-zone-trust]q
[FW1]firewall zone dmz
[FW1-zone-dmz]add interface GigabitEthernet 0/0/2
[FW1-zone-dmz]q
[FW1]firewall zone untrust
[FW1-zone-untrust]add interface GigabitEthernet 0/0/3
[FW1-zone-untrust]q
注:区域里必须要有唯一的安全级别,相应的接口要加入到区域,可以是物理接口和逻辑接口(Vlanif、Tunnel)。
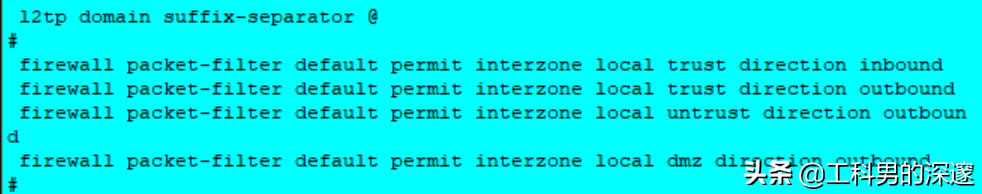
这时候3个域就建立好了,但是域与域之间是不通的,因为域之间默认是拒绝的。但是从防火墙到内网、DMZ、UnTrunst区域内设备又是通的。
防火墙默认Trust区域设备到内网网关是互通的,但是DMZ区域内设备到防火墙是拒绝访问的。
Display this查看默认的包过滤规则
4测试防火墙到各域设备
从防火墙到各区域设备,都能通讯;
[FW1]ping 192.168.1.10
[FW1]ping 192.168.80.10
[FW1]ping 10.1.1.11
全部都能互通;

5配置防火墙的域间包过滤策略
(1)配置内网用户访问DMZ内WEB服务器
配置内网访问DMZ服务器策略
[FW1]policy interzone trust dmz outbound
[FW1-policy-interzone-trust-dmz-outbound]policy 5
[FW1-policy-interzone-trust-dmz-outbound-5]policy source 192.168.1.10 0//只放行单个地址;
[FW1-policy-interzone-trust-dmz-outbound-5]policy destination 192.168.80.10 0//只允许访问单个服务器;
[FW1-policy-interzone--trust-dmz-outbound-5]policy service service-set http//配置允许通过浏览器访问
[FW1-policy-interzone--trust-dmz-outbound-5]policy service service-set icmp//配置表示允许ping命令;
[FW1-policy-interzone-trust-dmz-outbound-5]action permit
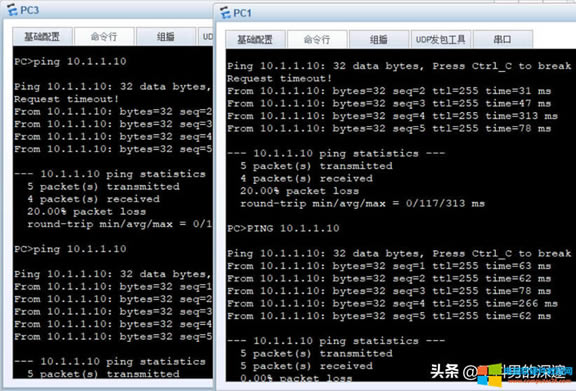
测试连通性
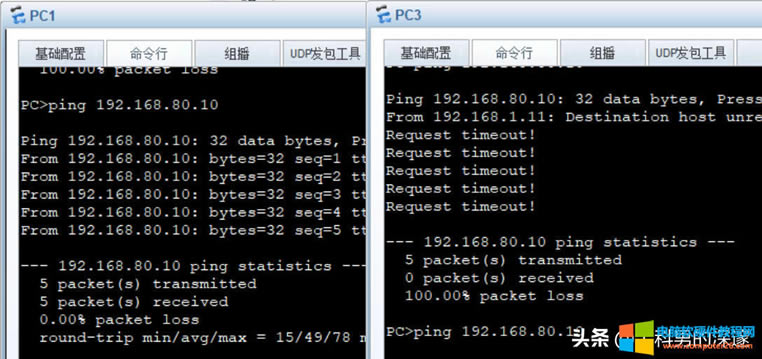
若内网有多个VLAN,如何配置呢?
(2)内网交换机SW1配置vlan10,vlan20,并将端口划入对应的VLAN当中。
[Huawei]sysname SW1
[SW1]vlan batch 10 20
[SW1]interface GigabitEthernet 0/0/1
[SW1-GigabitEthernet0/0/1]port link-type access
[SW1-GigabitEthernet0/0/1]port default vlan 10
[SW1-GigabitEthernet0/0/1]q
[SW1]interface GigabitEthernet 0/0/2
[SW1-GigabitEthernet0/0/2]port link-type access
[SW1-GigabitEthernet0/0/2]port default vlan 20
[SW1-GigabitEthernet0/0/2]q
[SW1]interface GigabitEthernet 0/0/24
[SW1-GigabitEthernet0/0/24]port link-type trunk
[SW1-GigabitEthernet0/0/24]port trunk allow-pass vlan 10 20
[SW1-GigabitEthernet0/0/24]q
(3)配置防火墙,配置子接口实现VLAN之间的互相访问。
[FW1]interface GigabitEthernet 0/0/1
[FW1-GigabitEthernet0/0/1]undo ip address 192.168.1.254 24
[FW1]interface GigabitEthernet 0/0/1.10
[FW1-GigabitEthernet0/0/1.10]vlan-type dot1q 10
[FW1-GigabitEthernet0/0/1.10]ip address 192.168.1.254 24
[FW1-GigabitEthernet0/0/1.10]q
[FW1]interface GigabitEthernet 0/0/1.20
[FW1-GigabitEthernet0/0/1.20]vlan-type dot1q 20
[FW1-GigabitEthernet0/0/1.20]ip address 192.168.2.254 24
[FW1-GigabitEthernet0/0/1.20]
(4)在防火墙上配置子接口实现VLAN互通,需要将子接口添加到区域中:
[FW1]firewall zone trust
[FW1-zone-trust]add interface GigabitEthernet 0/0/1.10
[FW1-zone-trust]add interface GigabitEthernet 0/0/1.20
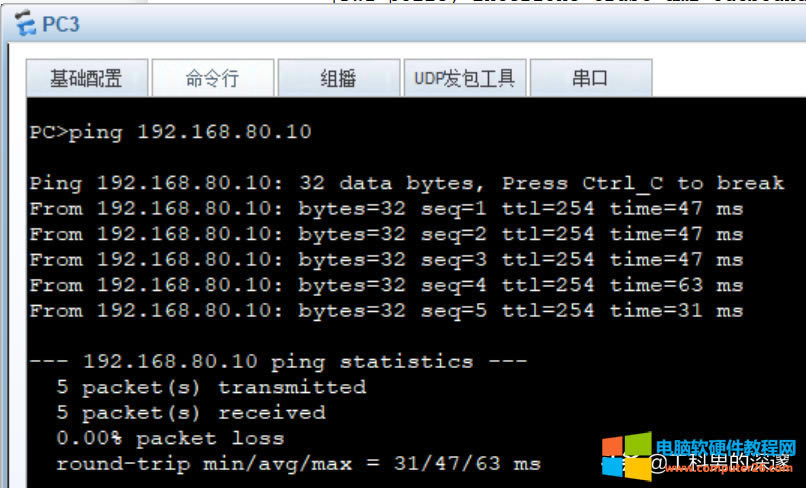
(5)测试
放行192.168.2.10访问DMZ服务器
[FW1]policy interzone trust dmz outbound
[FW1-policy-interzone-trust-dmz-outbound]policy 5
[FW1-policy-interzone-trust-dmz-outbound-5]policy source 192.168.2.10 0
[FW1-policy-interzone-trust-dmz-outbound-5]q
[FW1-policy-interzone-trust-dmz-outbound]q
测试
……